12 Years of FLOSS License Compliance: A Historical Perspective
Bradley M. Kuhn
Wednesady 26 October 2011
My History
Worked my first GPL enforcement case in 1999 (as FSF volunteer).
Started working for FSF in 2000 (until 2005).
Worked at SFLC from 2005–2010.
Now: Executive Director of Software Freedom Conservancy & on Board of Directors of the FSF.
Plurality of my time since 1999 has been spent on GPL enforcement.
Nature of Free Software Community
Through the eyes of a GPL enforcer …
- The Free Software Community is separated into two equally important groups:
- The permissively licensed, who use social pressure to liberate code.
- The copyleft licensed, whose license requires liberation.
Mine are the stories of the latter.
On Requirement By License
- Social pressure does work …
- … and should be used (and is), even for copylefted software.
- … enforcement is a last resort.
- GPL == Constitution of Software Freedom Land.
- a “written down” embodiment of core principles.
- GPL’s a detailed implementation of the four freedoms:
- freedom to run and study.
- freedom to improve.
- freedom to share.
- freedom to share improvements.
How GPL Works (Theoretically)
Copyright: the internationalized standard for authors’ controls over works.
Use copyright license to grant permission.
Make permission conditional on giving your downstream the four freedoms.
This is the copyright law hack of copyleft.
Copyright rules require compliance with the license.
How GPL Works (In Reality)

- What do you do when someone violates?
- (and social pressure for compliance fails)?
- Copyright enforcement
- … (yes, similar stuff to what the MPAA does: EEP!)
- … but for a good cause: the four freedoms.
- “using the tools of the oppressor against the oppressor”
Earliest Copyleft Programs
GNU Emacs: was the first GPL’d program.
AFAIK Emacs’ copyleft never been violated.
Second Copyleft Program

- GCC: second GPL’d program.
- much more interesting to proprietary software companies.
- So, who was the first GPL violator?
The NeXT Shall be First
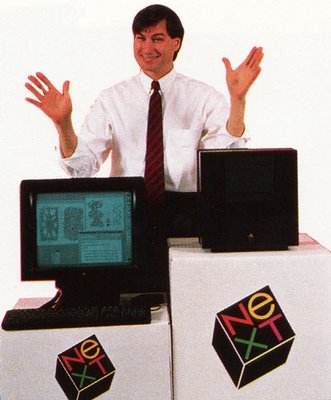
- Objective-C front end.
Earliest Post I Could Find
Path: utzoo!utgpu!jarvis.csri.toronto.edu!mailrus!cs.utexas.edu!usc!apple!bbn!bbn.com!bpalmer
From: bpal…@bbn.com (Brian Palmer)
Newsgroups: gnu.misc.discuss
Subject: Objective Gnu?
Message-ID: <5768@bbn.COM>
Date: 19 Sep 89 15:36:16 GMT
In “The NeXT Book” by Bruce Webster, he says: (page 134):
Objective C is based on the Gnu C compiler developed by Richard Stallman. Release 0.9 has merged the Objective C syntax with the the Gnu C compiler to speed up compilation and to produce faster, more efficient code.
Are they using FSF software in their product? Or is Webster just badly explaining the situation … and Objective C is just preprocessing and passing C to gcc.
Otherwise Gang, I see a Copyleft violation right?
Brian
NeXT Answers
Path: utzoo!utgpu!jarvis.csri.toronto.edu!rutgers!apple!gem.mps.ohio-state.edu!tut.cis.ohio-state.edu!NEXT.COM!Matthew_Self
From: Matthew_S…@NEXT.COM
Newsgroups: gnu.gcc
Subject: Objective-C front end for GCC from NeXT
Message-ID: <8909210104.AA14825@batcomputer.NeXT.COM>
Date: 21 Sep 89 01:01:50 GMT
Sender: dae…@tut.cis.ohio-state.edu
In response to Steve Simmons’ inquiry about an Objective-C front-end for GCC, NeXT will be making our modifications to GCC for Objective-C available very soon.
Once GCC–1.36 is released (any day now), I will create a patch kit which will be announced on this mailing list. (The modifications are very small.)
Matthew Self
Tar Wars

A long time ago, in a city far far away, the Empires had taken GNU tar and placed it into proprietary backup solutions. A small band of freedom fighters enforced the GPL to liberate users who were oppressed by the proprietary nature of GPL violators.
Tar Wars
Tape backup systems essential in late 1990s.
Many companies made forks of GNU Tar, and violated.
Sysadmins were good at finding these violations.
All but one violator came into compliance.
Court May Not Mandate Source Release
Last GNU tar enforcement I ever did was circa mid–2002.
Company decided to remove tar & rewrite rather than compliance.
Let’s sue!
Lawyers told me courts are unlikely to order a source release as a remedy.
- Courts usually give money and an injunction
- Company already gave latter of their own accord (de-facto)
Coalition of the Willing

Spring 2003: dozens of reports on WRT54G.
Discussions begin with Cisco (who’d bought Linksys just weeks before)
Story hits slashdot on 2003–06–08
- FSF puts together group to do enforcement.
- key members: Erik Andersen (BusyBox) & Harald Welte (Linux)
Compliance Takes Soooo Long
FSF represents the coalition.
Broadcom is discovered as upstream.
WRT54G source is released (but wireless driver kept proprietary).
Broadcom argues FCC prohibits; FSF agrees not to pursue (can’t really anyway).
WRT54G releases spawns OpenWRT community.
Harald is frustrated.
GPL-violations.org

FSF was initially shy about lawsuits.
Harald disagreed with FSF strategy (in hindsight, he was right).
launches multiple lawsuits in Germany (about 8 between 2005–2008).
Quite successful, although has in some cases, courts only grant injunction.
GCC Redux, 2003–2005
Embedded systems become major part of industry.
GCC is the best compiler.
Many companies start making GCC-based toolchains.
Focus of post-WRT54G enforcement at FSF.
Funding Crisis for Enforcement
FSF had hoped to raise funds “certifying compliance”.
You can’t break even on this for less than $10,000/release.
No one is willing to pay (still true today, AFAICT).
Those who’d know enough to buy services think they’ll get away with violations anyway.
Money
No one in non-profits is getting rich from this.
- Who should pay for enforcement:
- Those who comply or those who violate?
- Individual donors?
There must be a deterrent.
Non-profit enforcement == accountability.
Confidentiality is something violators ask for.
Enforcement Corruption: MySQL

Proprietary relicensing (by holding all copyright).
GPL enforcement with profit as its primary (and only?) goal.
MySQL would shake down GPL users to buy proprietary licenses they didn’t need.
I wish I’d identified this as corruption sooner.
Embedded Violations Prevalent
- Erik Andersen becomes exasperated by mid–2006.
- post-Linksys compliance, router & NAS market is a violation haven.
Erik asks for help.
Conservancy becomes his enforcement agent (& receive some others’ © assignment)
- Conservancy has had > 100 GPL violations queued for action since 2007.
- Conservancy’s list is now > 300
The Era of GPL Litigation
- Lawsuits become undeniably necessary.
- Dan Ravicher & Aaron Williamson file some in USA: for Conservancy & Erik.
- Focus is to settle:
- More than anything else, we want full compliance …
- … on all GPL’d and LGPL’d components …
- … judge is unlikely to grant us all that …
- … so we work hard to settle on that request …
- … taking extra money & injunctions only as a consolation prize.
Linksys Redux
2003–2004: all embedded consumer devices are VxWorks.
Circa late 2004, BusyBox/Linux & GNU/Linux slowly becomes the Linksys default again.
FSF finally gets fed up and sues.
One wonders: Why don’t these companies just come into compliance before getting sued?
Challenges of Modern Compliance
- Saavy violators meant intelligent discussion.
- Jobs knew just what he was trying to get away by proprietarizing Objective C.
- Clueless violators means difficult conversations:
- Me: “Your software violates GPL.”
- Them: “We make hardware.”
- Me: “I know, but it has software in it. Our members’ software. Under the GPL.”
- Them: “No, it doesn’t. We make hardware.”
- Me: “But your firmware download…on your website…that’s software.”
- Them: “Oh, that’s not ours. We got that from someone. Nothing to do with us.”
- Having the above conversation across four phone calls every two months is why I seem so insane most of the time.
The Upstream Problem

When I said that I was king of forwards, you got to understand that I don’t come up with this stuff. I just forward it along. You wouldn’t arrest a guy who was just passing drugs from one guy to another.
— Michael Scott, The Office (USA Version)
Suppliers Bully OEMs, AFAICT
I’d be the worst police officer in the world.
- No one ever turns “states’ evidence”
- … at least they don’t for me, anyway.
Me: “Please, just tell me on the record your supplier violated when distributing to you.”
Them: “We’ll work with our upstream to get into compliance.”
Embedded Device Software Freedom
Sure, I’ve got the sources.
But, can I build it in the same way the company did?
If I get it built, can I install it?
By the time I get all that working, will the device be discontinued?
Will they get away with it if they do, only to violate in the next product line?
In the age of the embedded device, copyleft seeks to answer these questions correctly.
GPL Predicted this Problem
- Even in 1991, RMS made sure GPLv2 handled this.
GPLv2: More than Just Source
For an executable work, complete source code means all the source code for all modules it contains, plus any associated interface definition files, plus the scripts used to control compilation and installation of the executable.
(emphasis mine)
GPLv2: More than Just Source
“the scripts to control…” gets us close.
It handles most of the issues.
- I even argued it includes authorized install information.
- Unfortunately, RMS gave in on that one.
GPLv3: Installation Information
“Installation Information” for a User Product means any methods, procedures, authorization keys, or other information required to install and execute modified versions of a covered work in that User Product from a modified version of its Corresponding Source. The information must suffice to ensure that the continued functioning of the modified object code is in no case prevented or interfered with solely because modification has been made.
If you convey an object code work under this section in, or with, or specifically for use in, a User Product, and the conveying occurs as part of a transaction in which the right of possession and use of the User Product is transferred to the recipient in perpetuity or for a fixed term (regardless of how the transaction is characterized), the Corresponding Source conveyed under this section must be accompanied by the Installation Information.
(emphasis mine)
GPLv3: Installation Information
In my view, just clarifies GPLv2’s terse wording.
In any event, it makes it certain.
- Users of device can modify and upgrade their devices …
- … as it should be.
This is one of the reasons projects should upgrade to GPLv3.
Today.
- I continue enforcement for Conservancy.
- new reports each week.
Matthew Garrett: Android device compliance.
FSF’s queue as long as Conservancy’s.
Constant Vigilance!
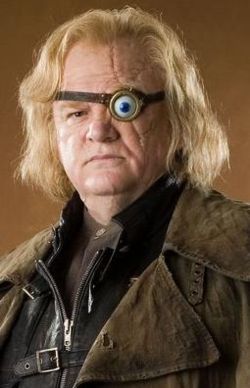
GPL Violations are everywhere.
- My only recourse is …
- Constant Vigilance!
- BTW, I’ll take an even money bet for (almost) any amount:
- Give me an hour and an Internet connection …
- & I’ll find you a GPL-violating embedded firmware I’ve never seen before.
More Info / Talk License
- URLs / Social Networking / Email:
- Conservancy: sfconservancy.org & @conservancy
- Me: ebb.org/bkuhn & @bkuhn (identi.ca only)
- FSF Licensing Site: fsf.org/licensing
- Report GPL violations: <compliance@sfconservancy.org>
- Slides at: ebb.org/bkuhn/talks & gitorious.org/bkuhn/talks (source)
Presentation and slides are: Copyright © 2008, 2009, 2010, 2011 Bradley M. Kuhn, and are licensed under the Creative Commons Attribution-Share Alike (CC-By-SA) 3.0 United States License. 
Some images included herein are ©’ed by others. I believe my use of those images is fair use under USA © law. However, I suggest you remove such images if you redistribute these slides under CC-By-SA-USA 3.0.